HTB: Meow Walkthrough

Overview
Difficulty: Easy
- Operating System: Linux
- Objective: Capture flag via Telnet
- Tools Used:nmap,telnet,openvpnPrepared by Araiz Naqvi
Scanning using Nmap
Started with a nmap scan to get information about whether telnet was running on port 23 as mentioned in the task.

And, it is!
Accessing Telnet at 10.129.109.246
Now, let’s telnet into said IP.
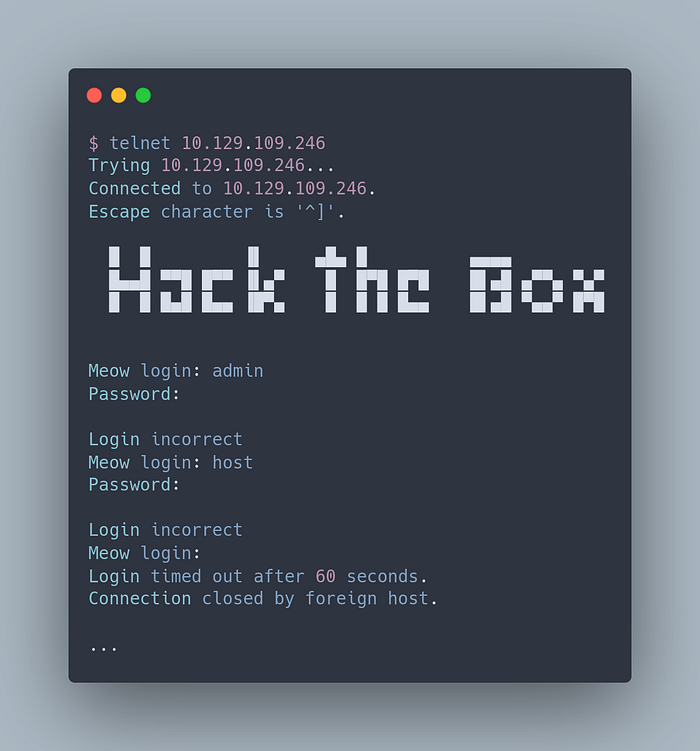
I tried a bunch of usernames but nothing seemed to work.
After a little research and hint from an answer in the machine it is clear that maybe `root` as the username will do the trick. So, let’s give it a shot.

Flag Retrieval
Let’s start by listing the content on the target:

Next, we will cat the content of flag.txt as:
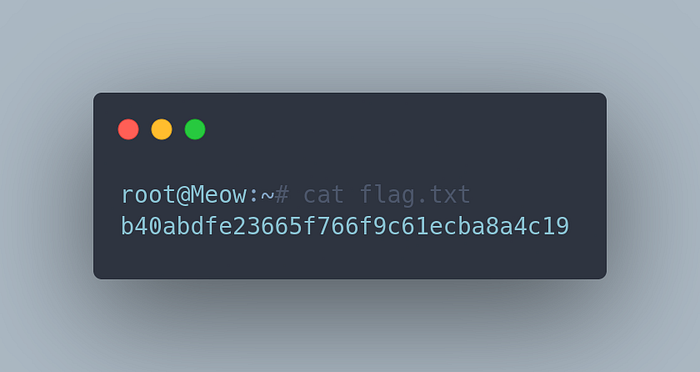
Flag
The flag is b40abdfe23665f766f9c61ecba8a4c19.
Lessons Learned
- A lot of the times, services are configured for ease of access with one username that does not have a password or some easy password. This can easily be guessed as I did or even bruteforced and automated.
- The best way to mitigate this issue is place solid standards on passwords by not only maintaining long complex password but also changing them regularly. As for ease of use, a password manager can be used to receive the password like MFA to log in or out.
Comments
Post a Comment